Paving the Way for a Secure Web3 Future: The Forthcoming Launch of Keystone 3

As the spectrum of the Web3 landscape broadens, hardware wallets are evolving into crucial gateways to a rapidly growing digital ecosystem. Therefore, hardware wallets need to not only guarantee strong protection for your private keys but also deliver a tailored and seamless user journey into Web3.
**Keystone** has become a trusted partner for numerous crypto users globally, delivering unmatched security measures to protect their digital assets. However, our commitment goes beyond safeguarding digital assets; we’re dedicated to harmonizing our hardware with future developments, continually enhancing user experience. Whether you’re an experienced crypto trader or a newcomer to the digital asset market, Keystone will be your reliable companion through the Web3 universe.
So, what sets Keystone apart? Our ethos and mission are underpinned by three core principles: an unshakeable commitment to maximizing compatibility, a promise to serve as a reliable security partner for all software wallets, and an unwavering dedication to innovation that guarantees the safest haven for your crypto assets.
Additionally, it’s essential to note that these factors were more than mere considerations; they served as the guiding pillars during the development of Keystone 3. Each principle was thoughtfully incorporated, ensuring that Keystone 3 not only upholds these values but also exemplifies them in its design.
Let’s dive deeper!
Keystone’s Core Positioning
The essence of Keystone’s philosophy emphasizes maximizing compatibility. We perceive ourselves as a dynamic security partner for all software wallets. Our wide-ranging compatibility with various software wallets gives an added layer of protection to our users and a safety net against a single point of failure, should a software wallet service be discontinued or cease maintenance.
????????????We’ve launched an open QR code standard that can be leveraged by any hardware wallet team! Why? Security, transparency, compatibility.
— MetaMask ???????? (@MetaMask) December 10, 2021
Very excited to announce our integration with @KeystoneWallet!
Learn why here????https://t.co/gJ7ZFhAFLO
Core now supports @KeystoneWallet, an air-gapped QR code hardware wallet with a 4” touchscreen & a highly visual UX, giving users another option for cold storage.
— Core???????? | Avalanche (AVAX) Wallet & Portfolio (@coreapp) April 5, 2023
Download Core and connect with your Keystone today! ????????????https://t.co/XwZUjne66n pic.twitter.com/EWfwgSL1bR
Core Security Assumptions
The foundational bedrock of our hardware wallet lies in offline security, placing paramount importance on an air-gapped configuration. The connection between a hardware wallet and a companion app is of utmost importance, and we’ve determined that data transmission via **QR codes** offers significant security advantages over alternative methods. We also strongly believe that a premium user experience (UX) is inextricably intertwined with impeccable security.
7/
— Keystone Hardware Wallet (@KeystoneWallet) May 23, 2023
???? How Keystone QR Codes Work
???? We believe that QR codes, in addition to being safe, are the most transparent means of data transmission for air-gapped cold storage
???? https://t.co/lNV4rT9x56 pic.twitter.com/1cOu1HswTP
We perceive Keystone not just as a “hardware wallet,” but more accurately, as an “offline signer.” This designation enables us to focus on our primary mission — assisting users to sign transactions securely.
Instead of typing in an address, you can simply scan the QR code directly on your Keystone device to get the address. This method ensures the utmost security as this is an offline address, completely immune to the risks posed by potential hackers. No hacker, no matter how skilled, can alter this offline address.
The recent attacks on **Atomic Wallet, Binance, Stake** and other CEXs could have easily been thwarted with the use of Keystone.
it's going to keep getting bigger ????@AtomicWallet @gladkos tell your users to move their funds *now.* then shut all your infra down, turn off all logging, revoke everyones access to all systems, rotate all keys & hire a *professional* ffs https://t.co/WDEpf2UL50 pic.twitter.com/umtzjHwGlu
— Tay ???? (@tayvano_) June 3, 2023
1/????Many users' deposit and withdraw addresses in the CEX have been replaced by the hacker address because of malware explorer extensions. There have been hundreds of attacks on Binance, https://t.co/bsZOzOhmvl, Bitso and other 10+ CEXs since June, 2022. @WuBlockchain @evilcos
— X-explore (@x_explore_eth) June 8, 2023
Prioritizing User Input
What sets us apart in the hardware wallet industry is our pledge to progress in response to user input. Our steadfast dedication to refining all aspects of our product results in consistent improvements. Recognizing the need of our users for more dependable software and durable hardware, we’ve made the necessary upgrades accordingly.
Maximizing Attack Cost & Minimizing Trust
We continuously strive to build up the cost of potential attacks. While no system is entirely impervious to hacking, making an attack prohibitively costly can act as a formidable deterrent. Physical attacks on hardware wallets generally cost considerably more than remote ones, making our offline, air-gapped system an ideal solution.
The team also resonates with Satoshi Nakamoto’s vision of a trustless system for ensuring one’s digital asset safety. Built on the principles of openness and transparency, Keystone incorporates open-source firmware and hardware, making it possible for anyone to scrutinize, validate, and contribute to its evolution. Keystone Product Design Principles The product design philosophies of Keystone Hardware Walletblog.keyst.one
Taking Human Error into Consideration
We’re not just thinking about hackers and attacks — we’re factoring in human error, too. With the increasing number of individuals venturing into the crypto world, **the risk of loss due to human error grows**. Therefore, during the design of Keystone, we took this into serious consideration, incorporating safeguards such as a more sensitive 4-inch touchscreen to enable better transaction prompts and a superior typing experience.
What is blind signing?
— Keystone Hardware Wallet (@KeystoneWallet) December 5, 2022
Blind signing is a process where a user signs a transaction without knowing the details of it
This means that the user is blindly trusting the message sender/application which can lead to potential risks
Learn more ????https://t.co/51U8nW6iZQ
When Keystone 3?
![Don’t miss out on the action! Follow us on **Twitter** and **Medium** to stay updated with all the content and activities we will be rolling out in the coming weeks.]
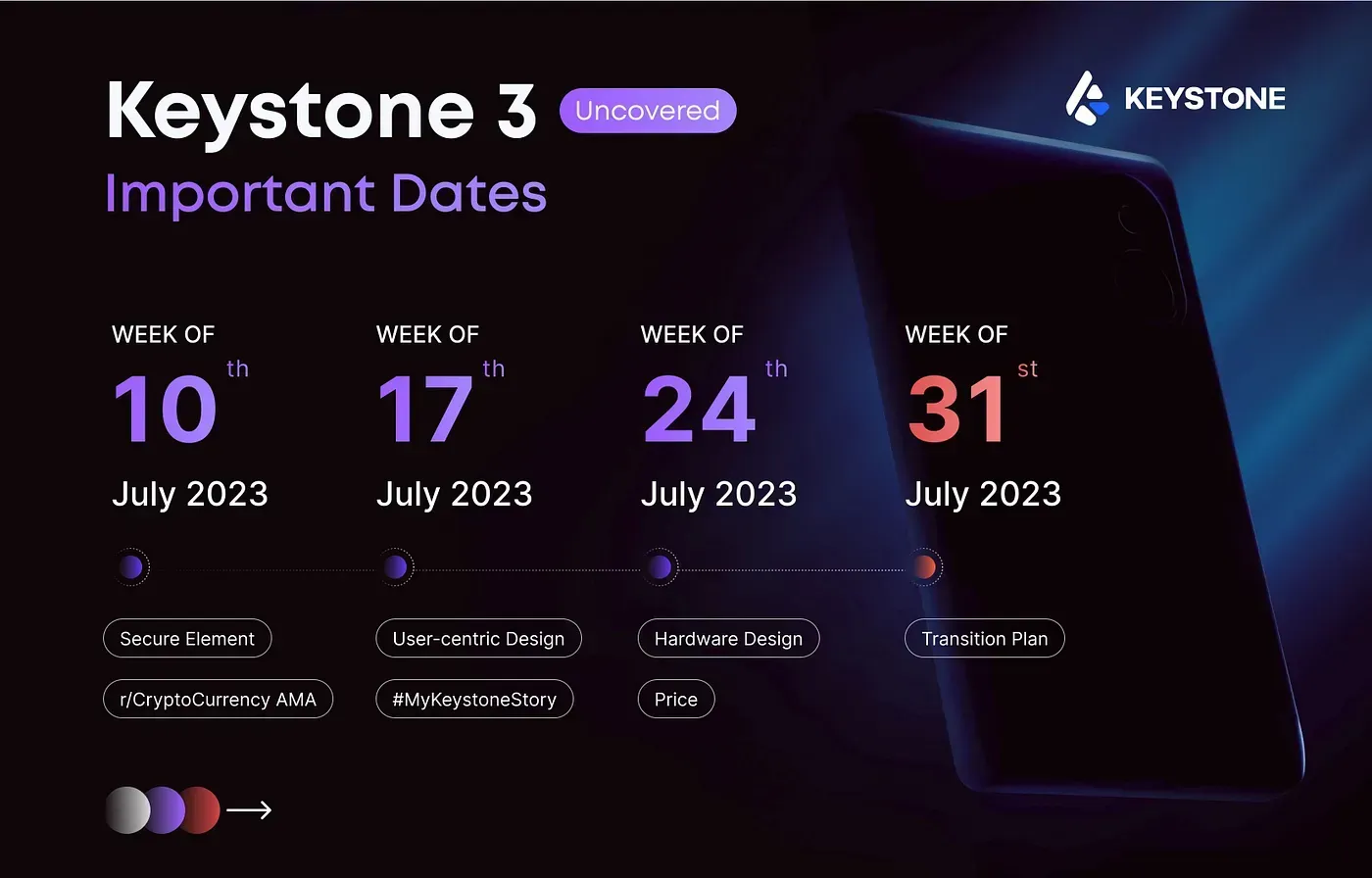
The launch of Keystone 3 is imminent, and we’re more excited than ever to continue this journey with you. As the embodiment of our core principles, we pledge to continue to offer unrivaled security and an unparalleled user experience.
Become part of our vibrant community and let’s make this journey even more exciting together. Your support fuels our innovation, so **get on the waitlist for Keystone 3** today and stay tuned for more details!
About Keystone
**Keystone** is an **open-source** airgap hardware wallet that utilizes an embedded system. To further enhance its security, the device is equipped with **three secure element chips. One of Keystone’s unique features is its ability to support **multiple recovery seed phrases, reducing the need to purchase multiple hardware wallet devices.
With the **primary aim** of maximizing security against potential threats, minimizing dependence, reducing human errors, and eliminating single points of failure, Keystone also places a strong emphasis on extensive interoperability. It is compatible with well-known software wallets such as **MetaMask** (both **Extension** and **Mobile** versions), as well as other premier software wallets like the **OKX Web3 Wallet, **Solflare, **Rabby**, and more.
